At Zadyn Group, we help organizations design, deploy, and operate modern cybersecurity programs that protect applications, data, and digital identities. Our services combine security advisory, technology procurement, implementation expertise, and managed security operations to deliver enterprise-grade cybersecurity capabilities.
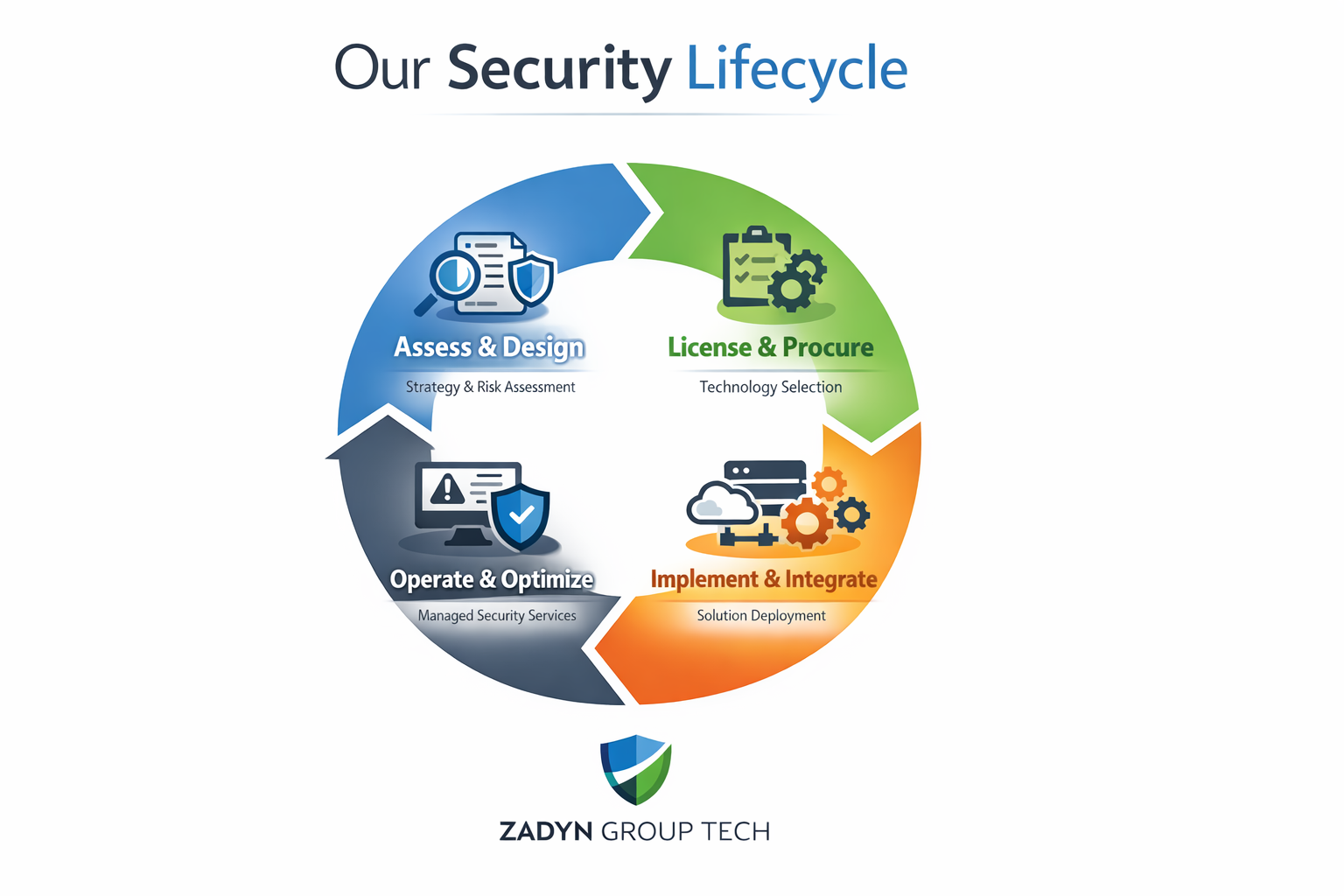
Our Security Delivery Model follows a structured lifecycle designed to support organizations from strategy through ongoing security operations.
Assess & Design
Strong cybersecurity programs begin with strategic planning and architecture design. Our advisory services help organizations identify risks, define security roadmaps, and build scalable security programs aligned with their business objectives and regulatory requirements. Through a structured assessment process, we evaluate an organization’s current security posture and provide practical recommendations to strengthen security frameworks and operational resilience.
Our services include cybersecurity strategy development, security architecture design, risk and threat assessments, security program maturity evaluations, security governance framework development, and Virtual CISO (vCISO) services that provide ongoing strategic security leadership and guidance.
License & Procure
Selecting the right cybersecurity technologies is essential for building an effective and scalable security architecture. Through our strategic vendor partnerships and reseller model, we help organizations evaluate, procure, and optimize enterprise security platforms that align with their technical requirements and business objectives. Our team provides guidance throughout the procurement process, ensuring organizations select the right solutions while maximizing the value of their technology investments.
Our capabilities include vendor advisory and platform selection, security platform licensing and renewals, vendor consolidation strategies, and contract optimization to help organizations streamline their security ecosystem and reduce operational complexity.
Implement & Integrate
Our engineering teams deploy and integrate cybersecurity solutions across complex IT environments, ensuring that security technologies are properly configured and aligned with existing infrastructure. We specialize in implementing solutions that support application security, data protection, and identity security, helping organizations strengthen their overall security posture while minimizing disruption to business operations. Through careful planning, integration, and optimization, we ensure that security platforms work effectively together to provide comprehensive protection across the organization’s digital environment.
Application & API Security Services
Applications and APIs are increasingly targeted by cyberattacks, making it critical for organizations to secure the systems that power their digital services and customer experiences. Our application security services help organizations protect web applications, APIs, and other customer-facing platforms by implementing security controls throughout the development and deployment lifecycle. We work closely with development and security teams to design and integrate security architectures that reduce vulnerabilities and strengthen overall resilience.
Our capabilities include web application security architecture design, web application firewall deployment, API security implementation, DevSecOps security integration, application security testing, vulnerability assessments, and penetration testing to identify and address potential weaknesses before they can be exploited.
Data Security Services
Protecting sensitive information is essential for maintaining customer trust, safeguarding intellectual property, and meeting regulatory compliance requirements. Our data security services help organizations protect critical data across hybrid, cloud, and on-premise environments by implementing comprehensive data protection strategies and technologies. We work with organizations to identify, secure, and manage sensitive data throughout its lifecycle while reducing the risk of unauthorized access or data loss.
Our capabilities include data discovery and classification, encryption architecture design, key management systems, hardware security module (HSM) integration, tokenization and data masking, and data loss prevention solutions that help organizations maintain visibility and control over their most valuable data assets.
Identity & Access Management Services
Identity has become the primary security perimeter in modern digital environments as organizations increasingly rely on cloud services, remote access, and digital customer experiences. Our identity security services help organizations securely manage and protect user identities while maintaining seamless and frictionless access to applications and systems. We design and implement identity architectures that strengthen authentication, enforce access controls, and improve user experience across enterprise environments.
Our capabilities include IAM architecture and implementation, Customer Identity and Access Management (CIAM), Single Sign-On (SSO), Multi-Factor Authentication (MFA), passwordless authentication, identity orchestration, and Privileged Access Management (PAM) to help organizations control and secure access to critical systems and data.
Operate & Optimize
Cybersecurity requires continuous monitoring, operational oversight, and ongoing optimization to remain effective against evolving threats. Our managed security services help organizations maintain a strong security posture without the need to build large internal security teams. By providing proactive monitoring, threat detection, and operational support, we help ensure security technologies are functioning effectively and that potential threats are identified and addressed quickly.
Our managed security capabilities include Security Operations Center (SOC) monitoring, endpoint detection and response, threat intelligence monitoring, dark web monitoring, email security protection, security awareness training, and phishing simulation programs designed to strengthen organizational security awareness and resilience.
Respond & Recover
Cyber incidents are inevitable in today’s threat landscape, but effective preparation and response can significantly reduce their impact on business operations. Our incident response services help organizations quickly detect, contain, and recover from cybersecurity events while minimizing disruption and protecting critical assets. We work with organizations to establish response procedures, investigate potential breaches, and implement remediation strategies that strengthen long-term resilience.
Our services include incident detection and response, breach investigation and digital forensics, threat containment and remediation, business continuity planning, disaster recovery strategy development, and cyber resilience planning to help organizations prepare for and respond effectively to future security incidents.